Ever clicked on a suspicious link and immediately felt that wave of regret? Cybersecurity often becomes a priority only after something goes wrong. But in today’s digital landscape, waiting for a breach to happen is no longer an option. Businesses need to proactively safeguard their systems, and that’s where tools like firewalls, VPNs, and intrusion detection systems (IDS) come into play.
These tools form the backbone of modern cybersecurity strategies. In this article, we’ll break down what each tool does, how it works, and why it’s essential for protecting your business. Whether you’re an IT manager, a business leader, or a tech-savvy professional, understanding these tools is key to staying ahead of cyber threats.
What Are Firewalls and Why Are They Critical?
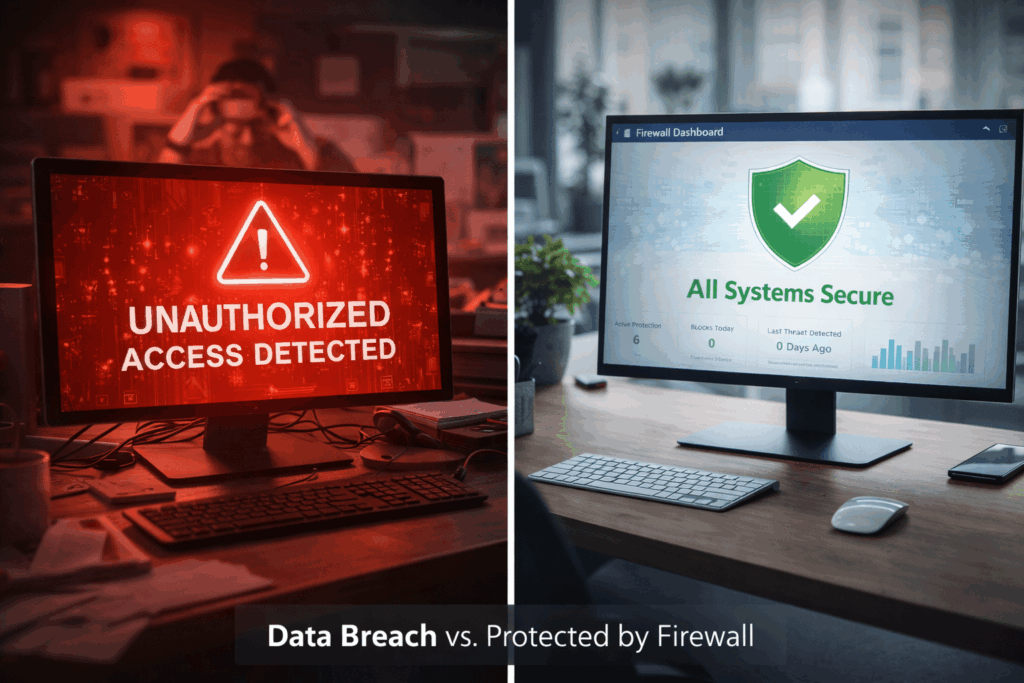
Think of a firewall as the security guard at the entrance of your business. It decides who gets in, who stays out, and what’s allowed to pass through. Firewalls are the first line of defense in cybersecurity, monitoring and controlling network traffic based on predefined security rules.
- Definition: Firewalls monitor and control incoming and outgoing network traffic, acting as a barrier between trusted internal networks and untrusted external networks.
- Types of Firewalls:
- Hardware Firewalls: Physical devices installed between your network and the internet.
- Software Firewalls: Applications installed on individual devices to filter traffic.
- Cloud-Based Firewalls: Scalable solutions hosted in the cloud, ideal for businesses with distributed teams.
- Why They Matter: Firewalls protect against unauthorized access, malware, and other cyber threats by filtering traffic and blocking malicious activity.
- Real-World Example: The 2017 Equifax breach, which exposed the personal data of 147 million people, could have been mitigated with proper firewall configurations and monitoring. Learn more about firewall best practices from CISA.
How Do VPNs Keep Your Data Secure?
Virtual Private Networks (VPNs) are essential for securing data in transit, especially in an era where remote work and hybrid teams are the norm. VPNs create an encrypted tunnel between your device and the internet, ensuring that sensitive data remains private and protected.
- Definition: VPNs encrypt your internet connection, masking your IP address and making it difficult for hackers to intercept your data.
- Use Cases:
- Remote workers accessing sensitive company data.
- Securing connections on public Wi-Fi networks, such as in coffee shops or airports.
- Ensuring privacy when accessing cloud-based applications like Microsoft 365 or Google Drive.
- Limitations: While VPNs are highly effective, they are not a standalone solution. They should be part of a broader cybersecurity strategy that includes firewalls and IDS.
What Is an Intrusion Detection System (IDS) and How Does It Work?
An Intrusion Detection System (IDS) is like a home security alarm for your network. It doesn’t block threats but alerts you to suspicious activity, giving you the chance to respond before damage is done.
- Definition: IDS monitors network traffic for malicious activity or policy violations and generates alerts when potential threats are detected.
- Types of IDS:
- Network-Based IDS (NIDS): Monitors traffic across the entire network.
- Host-Based IDS (HIDS): Focuses on monitoring activity on individual devices or servers.
- How It Works: IDS analyzes traffic patterns, compares them to known threat signatures, and flags anomalies for further investigation.
- Real-World Example: In 2021, an IDS helped a healthcare organization detect and mitigate a ransomware attack before it could encrypt critical patient data. Learn more about IDS standards from NIST.
How Do These Tools Work Together to Protect Your Business?
Firewalls, VPNs, and IDS are most effective when used as part of a layered cybersecurity strategy. This approach, known as defense in depth, ensures that even if one layer is breached, others remain to protect your systems.
- Layered Security: Imagine a medieval castle with walls, a moat, and guards. Firewalls act as the walls, VPNs as the secure pathways over the moat, and IDS as the guards alerting you to intruders.
- Relatable Example: A business using all three tools can block unauthorized access (firewall), secure remote employee connections (VPN), and detect unusual activity (IDS), creating a comprehensive security framework.
- Role of IT Services: Managed IT services, like those offered by CRES Technology, can help businesses implement and maintain these tools effectively, ensuring they work together seamlessly.
Conclusion
Firewalls, VPNs, and IDS are essential tools for modern cybersecurity. Firewalls block unauthorized access, VPNs secure data in transit, and IDS detects suspicious activity. Together, they form a robust defense against cyber threats.
Staying proactive in cybersecurity is critical to avoiding costly breaches. If you’re unsure whether your current tools are sufficient or working together effectively, expert guidance can make all the difference. At CRES Technology, we specialize in managed IT and cybersecurity services to help businesses protect their systems and data.
Are your cybersecurity tools working together to protect your business, or are there gaps in your defenses? Now is the time to evaluate and strengthen your strategy.
How we can help:
CRES Technology ensures to keep your network and data protected so that you can feel secure and confident.

Many of our clients were in danger of becoming a victims of cybersecurity attacks. They needed an IT security to help prevent attacks from ever happening and help them recover if an attack did happen. That’s where CRES Cybersecurity comes in.
With our extensive capabilities in cybersecurity and partnership with top cybersecurity software companies, we enable you to prevent cyber attacks, network exploitation, data breaches, phishing emails, and more. Our RMM audit assesses the health of your network and resources. We offer network penetration testing to prevent network exploitation, implement data loss prevention policies to prevent data breaches, and phishing email testing to teach your staff to identify phishing emails. CRES Technology implements state-of-the-art Endpoint Detection & Response solutions, allowing your company to be able to recover from any kind of damage caused by cybercriminals.
About Irfan Butt

CRES Technology – Founder and CEO
A strategic leader with over twenty years of progressive experience in Business Administration, Finance, Product Development, and Project Management. Irfan has a proven track record in a broad range of industries, including hospitality, real estate, banking, finance, and management consulting.