Cyberattacks are a daily reality for businesses of all sizes. From ransomware to phishing schemes, the sophistication and frequency of these threats have skyrocketed, leaving organizations scrambling to defend themselves. The consequences of being unprepared can be devastating: financial losses, reputational harm, and operational disruptions that can take weeks or even months to recover from.
That’s where a well-structured incident response plan comes in. Think of it as your organization’s playbook for handling cyber incidents. It’s not just about reacting to attacks but minimizing damage, ensuring business continuity, and learning from each incident to strengthen your defenses. At CRES Technology, we specialize in helping organizations like yours build and maintain robust cybersecurity strategies, so you’re not left vulnerable when (not if) a cyberattack occurs.
Why Is Incident Response Planning Critical for Modern Businesses?
Having an incident response plan isn’t a luxury—it’s a necessity. Let’s break down why:
- Rising cyber threats: Cybercriminals are more creative than ever. Ransomware attacks can lock down your systems until you pay a hefty ransom. Phishing emails can trick even the most cautious employees into revealing sensitive information. And let’s not forget insider threats—whether malicious or accidental, they can wreak havoc on your organization.
- Consequences of unpreparedness: Imagine waking up to find your company’s data encrypted, your operations at a standstill, and your customers losing trust in your ability to protect their information. The financial losses alone can be staggering, but the reputational damage and operational downtime can be even harder to recover from.
- The role of incident response: A well-prepared incident response plan acts as your safety net. It helps you contain the damage, recover faster, and maintain business continuity. Think of it as the difference between a small kitchen fire and your entire house burning down.
For a deeper dive into the growing cyber threat landscape, check out this NIST Cybersecurity Framework.
What Are the Key Components of an Effective Incident Response Plan?
Creating an incident response plan isn’t just about writing a document and calling it a day. It’s about building a comprehensive strategy that evolves with your organization’s needs. Here are the key components:
- Preparation: Start with the basics—establish clear policies, train employees to recognize threats, and conduct regular risk assessments. Preparation is your first line of defense.
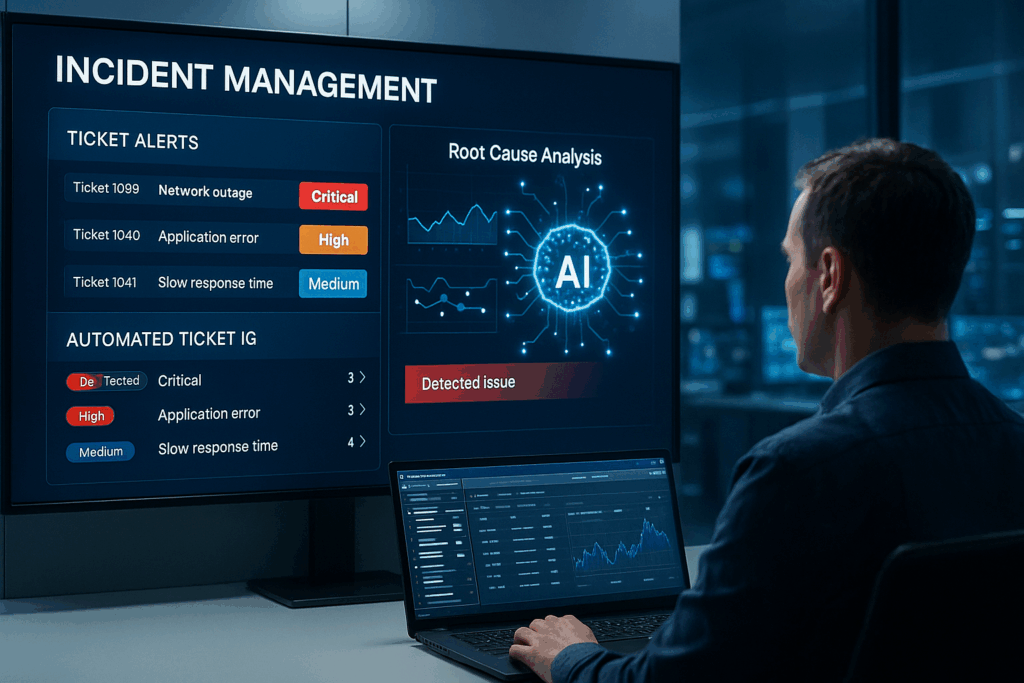
- Detection and Analysis: Use monitoring tools and threat intelligence to identify potential threats. The faster you detect an issue, the quicker you can act to mitigate it.
- Containment: Once a threat is identified, isolate affected systems to prevent it from spreading. Think of it as quarantining a virus before it infects the whole network.
- Eradication: Remove the threat entirely and address any vulnerabilities that allowed it to occur in the first place. This step ensures the problem doesn’t come back to haunt you.
- Recovery: Restore systems and data to normal operations. This might involve backups, system rebuilds, or even public communication, depending on the severity of the incident.
- Post-Incident Review: After the dust settles, analyze what happened. What worked? What didn’t? Use these insights to improve your plan and strengthen your defenses.
How Can You Test and Improve Your Incident Response Plan?
Even the best plans need regular testing and refinement. Here’s how you can ensure your incident response plan stays effective:
- Conduct tabletop exercises and simulated attacks: These exercises allow your team to practice their response in a controlled environment. It’s like a fire drill for your IT department—better to find gaps in your plan now than during a real attack.
- Regularly update the plan: Cyber threats evolve, and so should your response plan. Make it a habit to review and update your plan to address emerging risks.
- Involve all stakeholders: Incident response isn’t just an IT issue. Include legal, HR, and executive teams in your planning and testing to ensure everyone knows their role during an incident.
For guidance on conducting effective tabletop exercises, refer to this CISA resource.
What Role Does Cybersecurity Expertise Play in Incident Response?

Let’s face it: most organizations don’t have the time or resources to handle cybersecurity on their own. That’s where experts like CRES Technology come in. Here’s how we can help:
- Access to advanced tools: We provide cutting-edge threat detection and response tools that give you an edge over cybercriminals.
- Expert guidance: Building and maintaining an effective incident response plan can be overwhelming. Our team of experts can guide you every step of the way.
- 24/7 monitoring and support: Cyberattacks don’t follow a 9-to-5 schedule, and neither do we. Our round-the-clock monitoring ensures that threats are addressed as quickly as possible.
Conclusion
Cyber threats aren’t going away, but that doesn’t mean your organization has to live in fear. By investing in a robust incident response plan, you can minimize damage, recover faster, and build resilience against future attacks. Remember, preparation is key, so don’t wait for a crisis to start planning.
At CRES Technology, we’re here to help you navigate the complexities of cybersecurity. Whether you need assistance building your incident response plan or want to explore our managed IT services, we’re just a call away. Let’s work together to safeguard your organization and ensure you’re ready for whatever comes next.
How we can help:
CRES Technology ensures to keep your network and data protected so that you can feel secure and confident.

Many of our clients were in danger of becoming a victims of cybersecurity attacks. They needed an IT security to help prevent attacks from ever happening and help them recover if an attack did happen. That’s where CRES Cybersecurity comes in.
With our extensive capabilities in cybersecurity and partnership with top cybersecurity software companies, we enable you to prevent cyber attacks, network exploitation, data breaches, phishing emails, and more. Our RMM audit assesses the health of your network and resources. We offer network penetration testing to prevent network exploitation, implement data loss prevention policies to prevent data breaches, and phishing email testing to teach your staff to identify phishing emails. CRES Technology implements state-of-the-art Endpoint Detection & Response solutions, allowing your company to be able to recover from any kind of damage caused by cybercriminals.
About Irfan Butt

CRES Technology – Founder and CEO
A strategic leader with over twenty years of progressive experience in Business Administration, Finance, Product Development, and Project Management. Irfan has a proven track record in a broad range of industries, including hospitality, real estate, banking, finance, and management consulting.