Introduction
Ever accidentally sent a text to the wrong person and felt a wave of panic? Now imagine that text contained sensitive business data or personal information. That’s the kind of nightmare scenario data encryption is designed to prevent. In this article, we’ll explore what data encryption is, how it works, and why it’s essential for businesses and individuals alike. Whether you’re a tech enthusiast or someone just trying to keep their data safe, this guide will help you understand the critical role encryption plays in modern cybersecurity.
What Is Data Encryption?
Data encryption is the process of converting information into a coded format, making it unreadable to anyone who doesn’t have the proper decryption key. Think of it as scrambling a message so that only the intended recipient can make sense of it. Encryption is a cornerstone of modern cybersecurity, ensuring that sensitive data remains secure even if it falls into the wrong hands.
Why Is Encryption Important?
Encryption is not just a technical safeguard; it’s a necessity in today’s digital landscape. Here’s why:
- Protects sensitive information from cybercriminals: Encryption ensures that even if data is intercepted, it remains useless to unauthorized parties.
- Ensures compliance with data protection regulations: Laws like GDPR and HIPAA mandate encryption to protect personal and sensitive information. Non-compliance can lead to hefty fines.
- Builds trust with customers and stakeholders: Businesses that prioritize data security demonstrate their commitment to protecting customer information, fostering trust and loyalty.
Consider the 2017 Equifax breach, where sensitive data of over 147 million people was exposed. If robust encryption had been in place, the damage could have been significantly mitigated. This example underscores the critical role encryption plays in safeguarding data.
How Does Data Encryption Work?
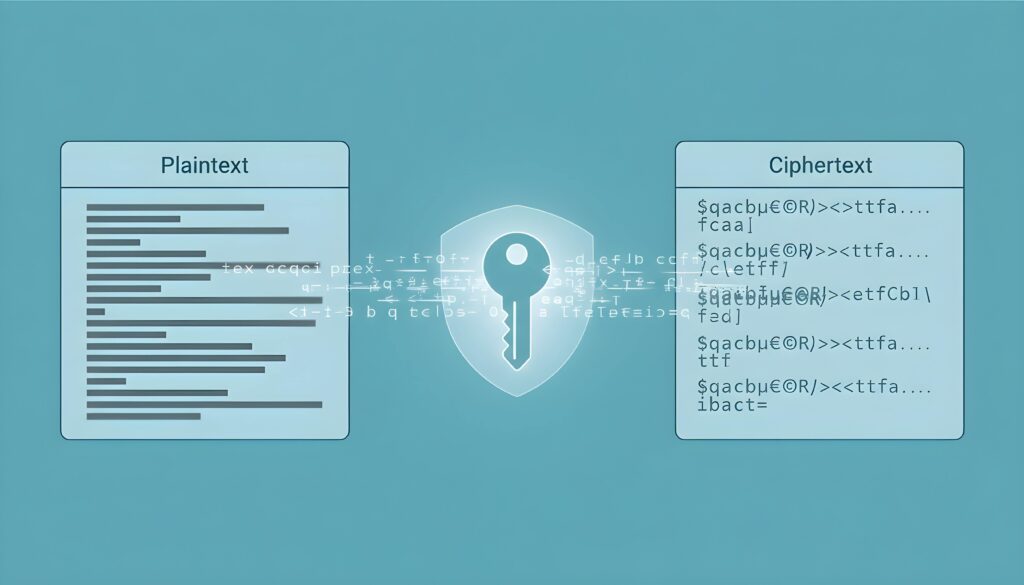
At its core, encryption works by transforming readable data (plaintext) into an unreadable format (ciphertext) using an algorithm and an encryption key. Only someone with the correct decryption key can convert the ciphertext back into plaintext.
Think of it like locking a message in a safe. The safe can only be opened with the correct key, ensuring that only the intended recipient can access the message. Encryption algorithms, such as AES (Advanced Encryption Standard), act as the safe, while the encryption key is the unique code needed to unlock it.
Modern encryption methods are highly sophisticated, relying on complex mathematical operations to ensure data security. This makes it nearly impossible for unauthorized parties to decipher encrypted data without the correct key.
What Are the Types of Data Encryption?
There are two primary types of data encryption, each suited to different use cases:
- Symmetric encryption: This method uses the same key for both encryption and decryption. It’s fast and efficient, making it ideal for encrypting large volumes of data. A common example is AES, widely used for securing sensitive information.
- Asymmetric encryption: This method uses a pair of keys—a public key for encryption and a private key for decryption. It’s often used in scenarios where secure key exchange is critical, such as email encryption or digital signatures. RSA is a popular example of asymmetric encryption.
Choosing between symmetric and asymmetric encryption depends on the specific needs of your organization. Symmetric encryption is best for securing data at rest, while asymmetric encryption is ideal for secure communication and data sharing.
It’s also worth mentioning hashing, which is often confused with encryption. Hashing converts data into a fixed-length string, but unlike encryption, it cannot be reversed. Hashing is commonly used for verifying data integrity, such as storing passwords securely.
What Are the Risks of Not Using Encryption?
Failing to encrypt sensitive data can have severe consequences, including:
- Increased vulnerability to cyberattacks: Unencrypted data is an easy target for hackers, who can exploit it through ransomware, phishing, or other malicious activities.
- Legal and financial repercussions: Non-compliance with data protection regulations can result in significant fines and legal action.
- Loss of customer trust and reputational damage: A data breach can erode customer confidence, leading to long-term harm to your brand.
Encryption is a critical component of a broader cybersecurity strategy. At CRES Technology, we help businesses implement comprehensive security measures, including encryption, to protect their data and maintain compliance with industry standards.
How Can Businesses Implement Encryption Effectively?
Implementing encryption may seem daunting, but with the right approach, it’s entirely manageable. Here are some actionable steps:
- Identify sensitive data: Determine which data needs encryption, such as customer information, financial records, or intellectual property.
- Choose the right tools and protocols: Use industry-standard encryption methods like TLS for securing web traffic or BitLocker for disk encryption.
- Train employees: Educate your team on encryption best practices, such as recognizing phishing attempts and securely sharing encrypted files.
- Regularly update and audit encryption methods: Cyber threats evolve, so it’s essential to keep your encryption protocols up to date and conduct regular security audits.
CRES Technology specializes in helping businesses implement encryption solutions as part of a comprehensive cybersecurity strategy. Our expertise ensures that your data remains secure and compliant with regulatory requirements.
Conclusion
Data encryption is a fundamental pillar of modern cybersecurity, protecting sensitive information from unauthorized access and ensuring compliance with data protection regulations. By prioritizing encryption, businesses can safeguard their data, build trust with customers, and mitigate the risks of cyberattacks.
If you’re unsure where to start, consider assessing your current encryption practices and identifying areas for improvement. Expert guidance can make all the difference, and CRES Technology is here to help. From implementing robust encryption solutions to developing a comprehensive cybersecurity strategy, we provide the expertise you need to protect your business in an increasingly digital world.
How we can help:
CRES Technology ensures to keep your network and data protected so that you can feel secure and confident.

Many of our clients were in danger of becoming a victims of cybersecurity attacks. They needed an IT security to help prevent attacks from ever happening and help them recover if an attack did happen. That’s where CRES Cybersecurity comes in.
With our extensive capabilities in cybersecurity and partnership with top cybersecurity software companies, we enable you to prevent cyber attacks, network exploitation, data breaches, phishing emails, and more. Our RMM audit assesses the health of your network and resources. We offer network penetration testing to prevent network exploitation, implement data loss prevention policies to prevent data breaches, and phishing email testing to teach your staff to identify phishing emails. CRES Technology implements state-of-the-art Endpoint Detection & Response solutions, allowing your company to be able to recover from any kind of damage caused by cybercriminals.
About Irfan Butt

CRES Technology – Founder and CEO
A strategic leader with over twenty years of progressive experience in Business Administration, Finance, Product Development, and Project Management. Irfan has a proven track record in a broad range of industries, including hospitality, real estate, banking, finance, and management consulting.